How to (honourlessly) win in Angry Words
Planted August 1, 2012
In my scarce free time I usually play Angry Words. For those who have never heard about it (quite unlikely if you’’re reading this article) Angry Words is basically a Scrabble that can be played online against different opponents. There are currently versions for Android and iPhone.
Recently, in May 2011, a security hole was reported in WhatsApp which left user accounts open for hijacking. Since May 2011 it has been reported that communications made by WhatsApp are not encrypted, and data is sent and received in plaintext, meaning messages can easily be read if packet traces are available. Together with the well-known storage of the full set of messages sent and received within the application (that can be easily cracked) led me to think if that was a concrete, disastrous development, or a generalized trend in most mobile applications. Therefore, I decided to see if it could be possible to do the same with Angry Words.
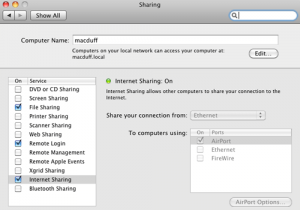
If you want to reproduce the steps in this article, you will need to set up your environment to sniff data from your mobile. There are many options to achieve this (install a cracked .apk or .ipa into your emulator and capture the data, root your Android device and capture the data with a sniffer…), but for me, the easiest one was to use my computer as a bridge for my phone, and use Wireshark to sniff the data. The process is quite simple: you just need to activate the “Internet Sharing” option, using your AirPort as a bridge to your ethernet connection (if you don’’t have an ethernet connection, you will surely still have the option to tether your phone). In “Configuration” - “Internet Sharing” proceed as shown in the following image:
You probably get the idea: the point is connecting the device to your computer and sniff the traffic from there. It is outside the purpose of this article to teach how to use Wireshark, but you can find many tutorials on the Internet. Basically, when your device is connected, start up Wireshark on your computer and attach to the Wi-Fi interface. You normally need to start Wireshark as the super-user in order to have enough rights to capture traffic. You can do this by typing sudo wireshark &.
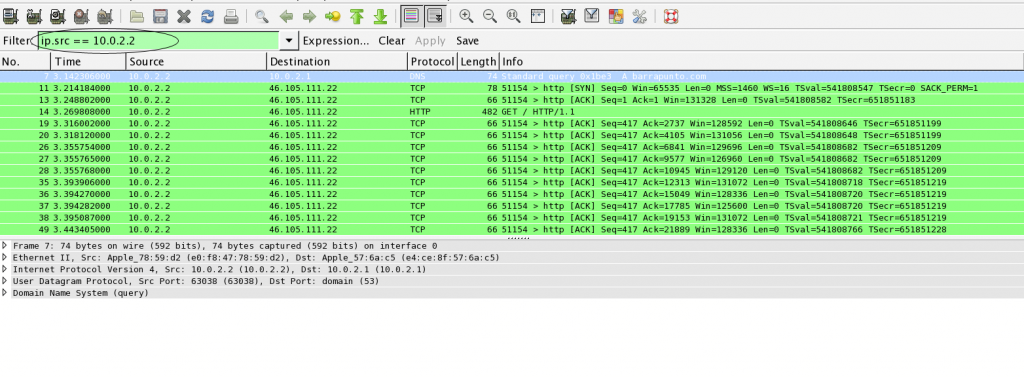
When this has been set up, and your device is connected to your computer, you will begin to filter all the packets. Since Wireshark does not discriminate between all the applications, it is a good idea to filter the packets that will be captured. For this purpose, you can create a filter using the following expression:
ip.src == xx.xx.xx.xx
ip.dst == xx.xx.xx.xx
The xx.xx.xx.xx value is the private IP that your phone has been assigned when connecting to your computer. In my case, this IP is 10.2.2.2
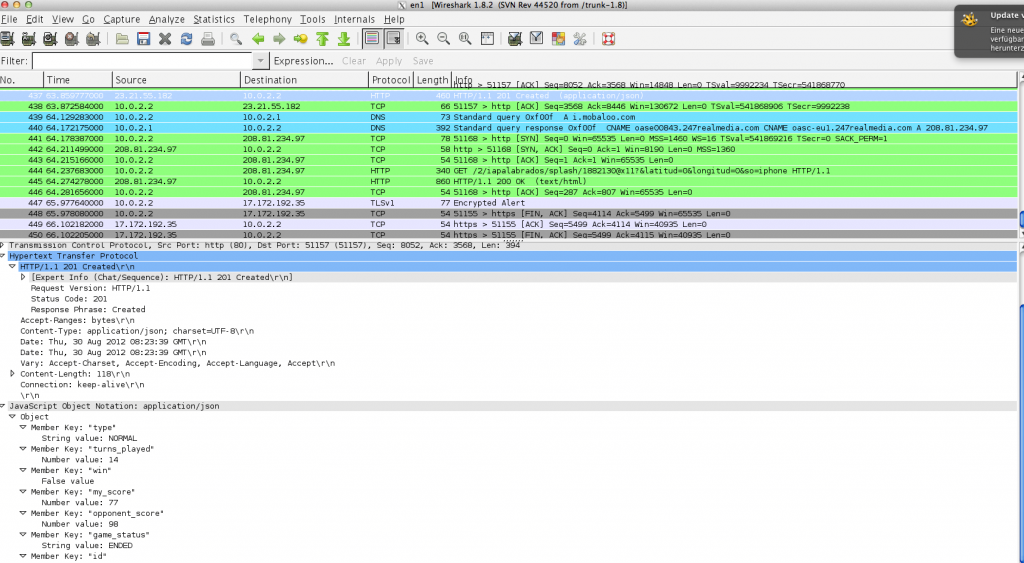
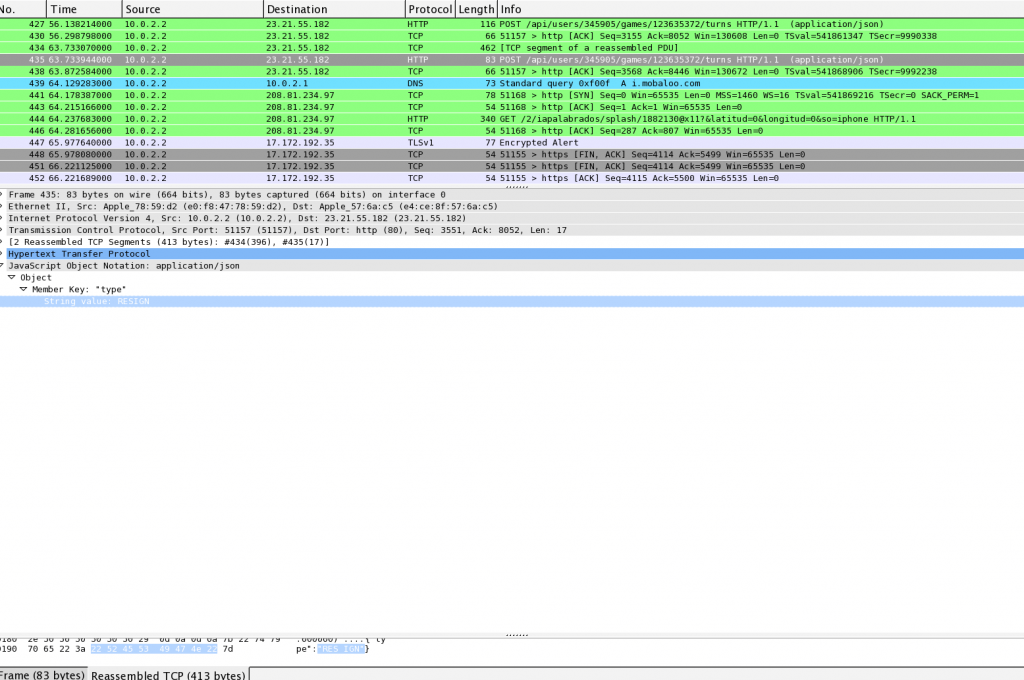
Now we will only display the packets corresponding to our device, so it''s time to play. By opening Angry Words and playing, we will see each request sent from the application (and received from the server). We will soon notice some issues:
- The application uses plain HTTP, no SSL in between. We can see all the requests sent as web requests. We can log in the application through Facebook Auth, or with our mail and password. If we use the second way, even the password is sent in plain text.
- All the information about each game is stored in the server (since we can access from different devices), which makes it a little bit more complicated to hack an already created game. But it can be achieved using a Man in the Middle attack, which is not hard if we are using our own computer as a proxy (also, we can decide whether a word is right or not).
- With each connection, a cookie value is created. This cookie value has to be sent within each request to validate all the requests.
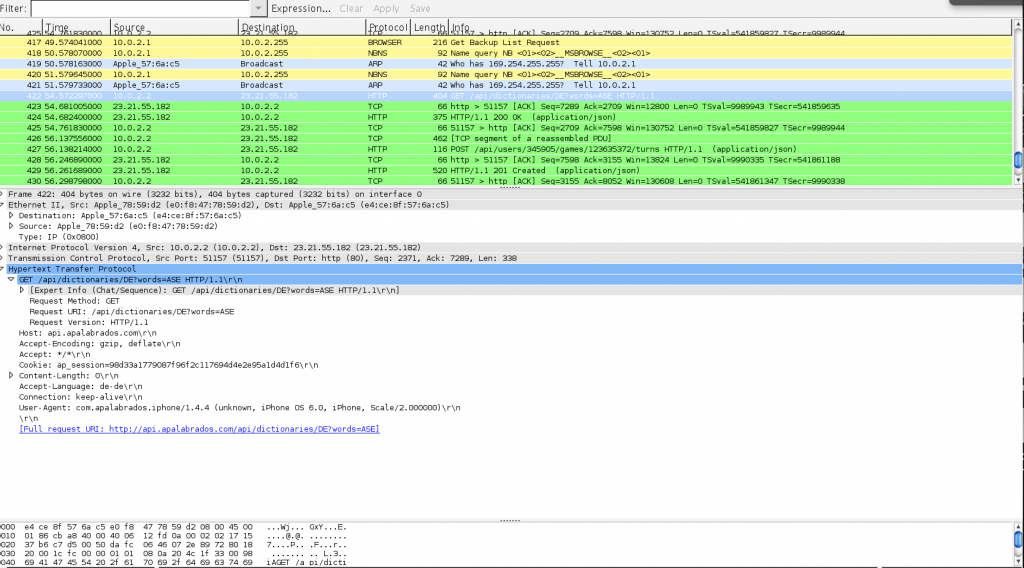
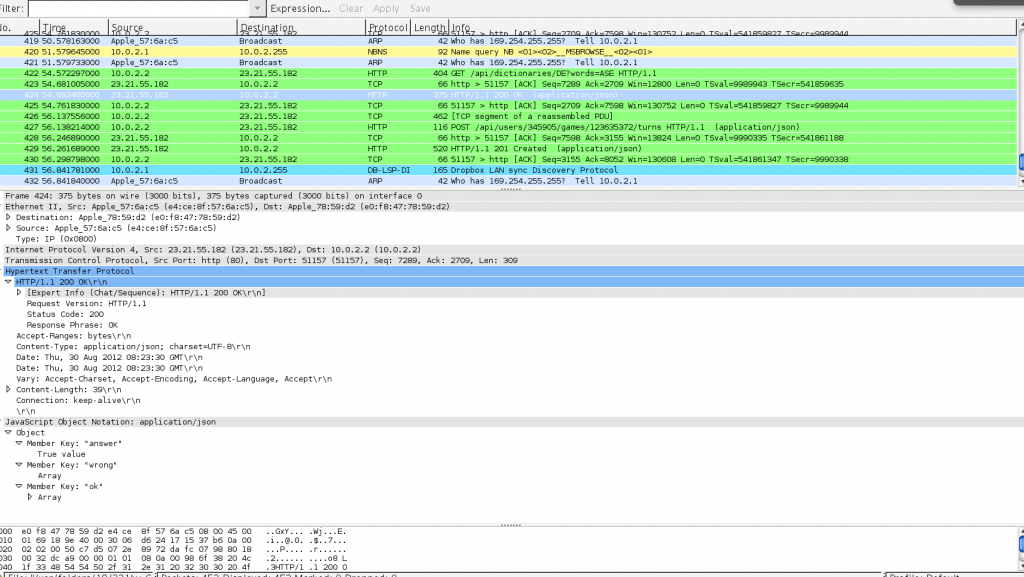
After sending a request to check if a word is right, we also receive all the information in plain text.
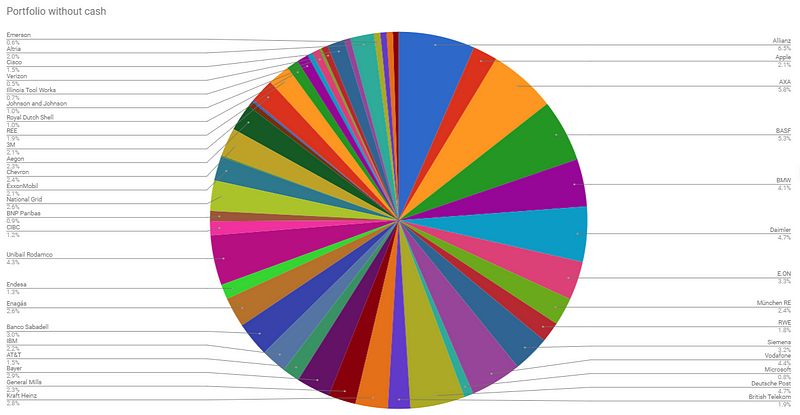
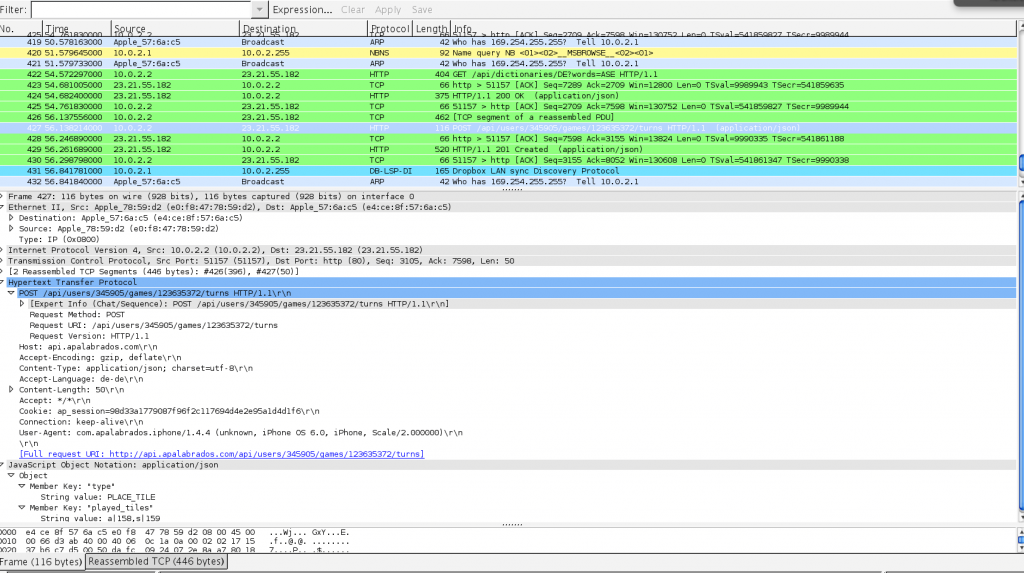
Here begins the interesting part: this is how we can send a tile to the server:
We also can see how to resign a game:
So, after analyzing all the game interactions, we can conclude the following:
- We can retrieve all the information about a user''s games by calling the following address: http://api.apalabrados.com/api/users/[USER_ID]/games .
- We can check the validity of a word using GET http://api.apalabrados.com/api/dictionaries/EN?words=wordtocheck . We will get a JSON {"answer":true,"wrong":[],"ok":["word"]} if the word is valid, or {"answer":false,"wrong":["word"],"ok":[]} if it is not.
- We can also pass or resign a game. By calling the address http://api.apalabrados.com/api/users/[USER_ID]/games/[GAME_ID]/turns , and adding either the value {"type":"PASS"} or {"type":"RESIGN"}, the server changes the status of the game.
- If we are connected to a WiFi network, doing a MiM and manipulating the data being sent back to the user is just trivial. Connecting through 3G or a GSM network makes things harder.
How can this be solved?
The obvious thing is to use an SSL connection, but this might require some changes and time in the server configuration. Also, to manipulate the requests (unless we automate it) some time is required, so creating a suitable timeout is also a good idea. I want to emphasize that, although the requests can be sent from a computer or automated programs, manipulating the data sent back is only possible through a wireless network. So, if you are suspicious that your AngryWords partner might be a hacker, disconnect your WiFi while you’’re playing against him or her.
You can contact me at my private email, or leave a message as a comment. If the post has been helpful for you, consider being nice and cite me if you use it.